| Name: | Type: | Short description: |
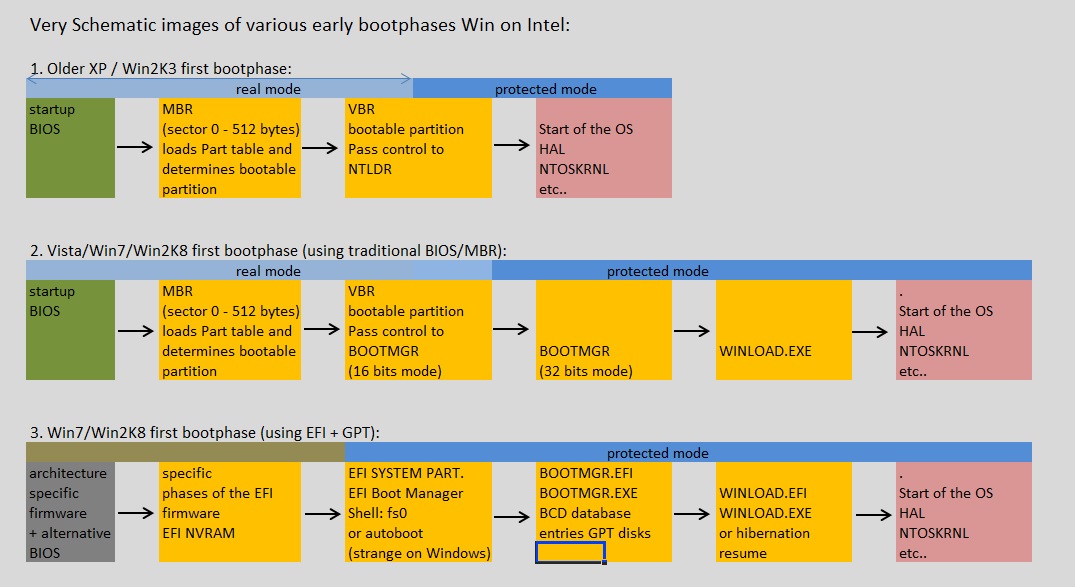
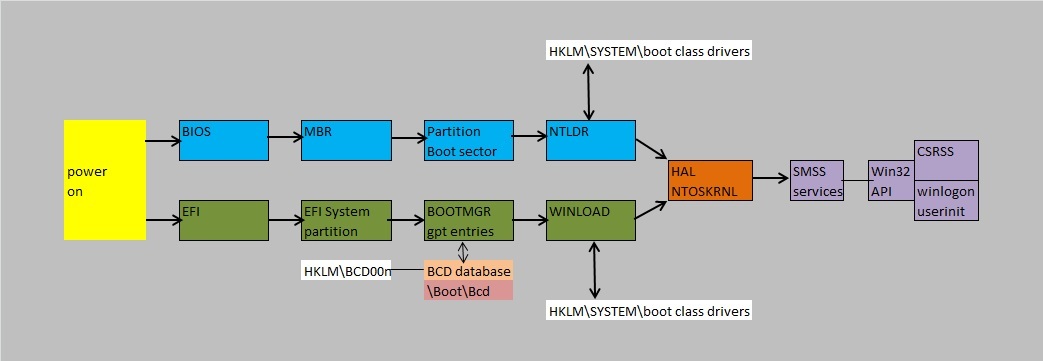
| VBoot Kit 1.0 | PoC | Presented in 2007. It was a PoC on Vista. The kit only patched files in memory to avoid detection on disk (as a DEMO PoC). Originally, it was activated from DVD, then used int13 to copy the MBR. Then it patched several systemfiles, most notably "bootmgr". Then, it relocated itself to a safer address, and patched the bootmgr bootmenu with it's own message (since it was a PoC). After making a user selected choice from the menu, it was shown that "winload" takes the preboot environment (setup by "bootmgr") for "granted" and for DEMO purposes, the kit patched a selection of other systemfiles. This was not detected in any way by Vista. Most notably, a hook in the NTOSKRNL was set, so that the kit could elevate other actions with systemprivileges. For further DEMO purposes, a "cmd" prompt under a Non-Admin user credential, was scheduled to elevate to "NT Authority\System". In 2009, VBoot kit 2.0 was presented, which was targeted for Windows 7. |
| TDSS/TDL3/TDL4 | Wild | "" |
| StuxNet/Duqu | Wild, but suspected to be created by Agencies |
|
| Mebroot/Torpig/Sinowal | Wild | "" |